SIW Network
Your one-stop solution for all your computer information needs.
SIW - Network Inventory Module
For more details please select one item from the following list:
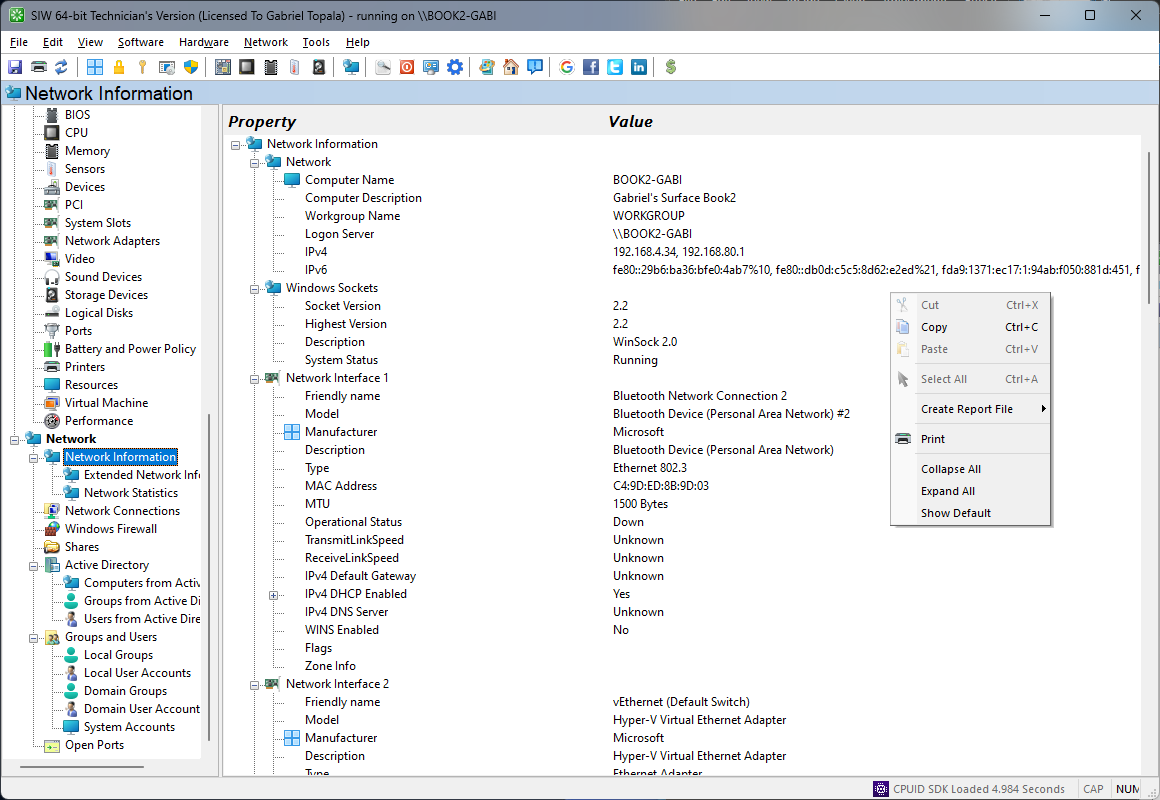
Basic Information about Network ConfigurationTop ↑
- Computer Name
- Workgroup or Domain
- Logon Server
- Socket Version
- Host Name
- IP Address
- Domain Name
- Adapter name
- MAC Address
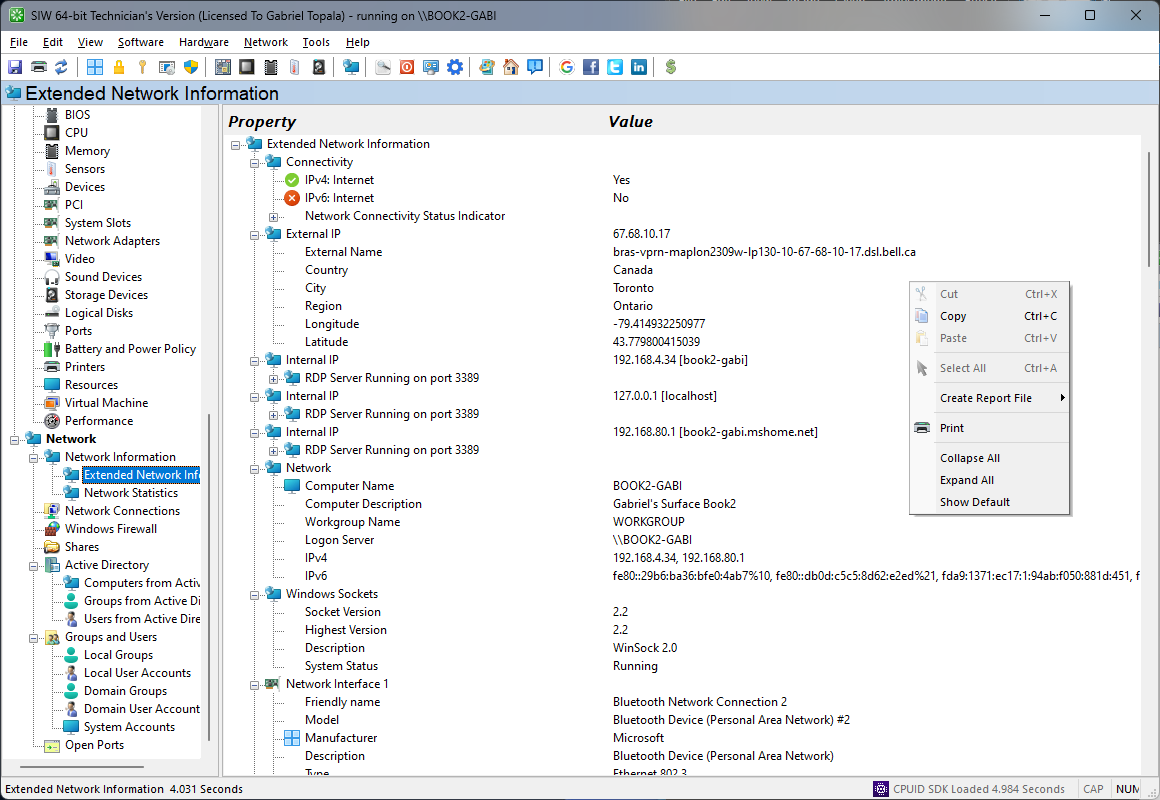
Extended Information about NetworkTop ↑
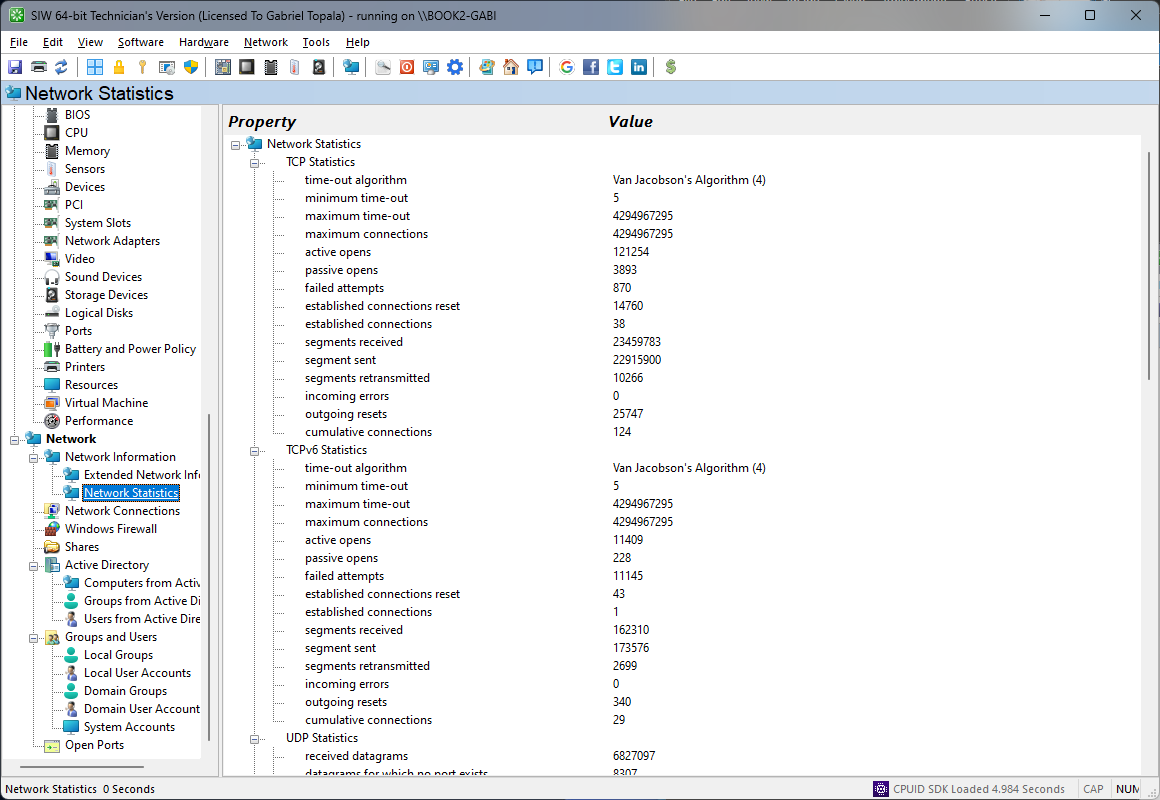
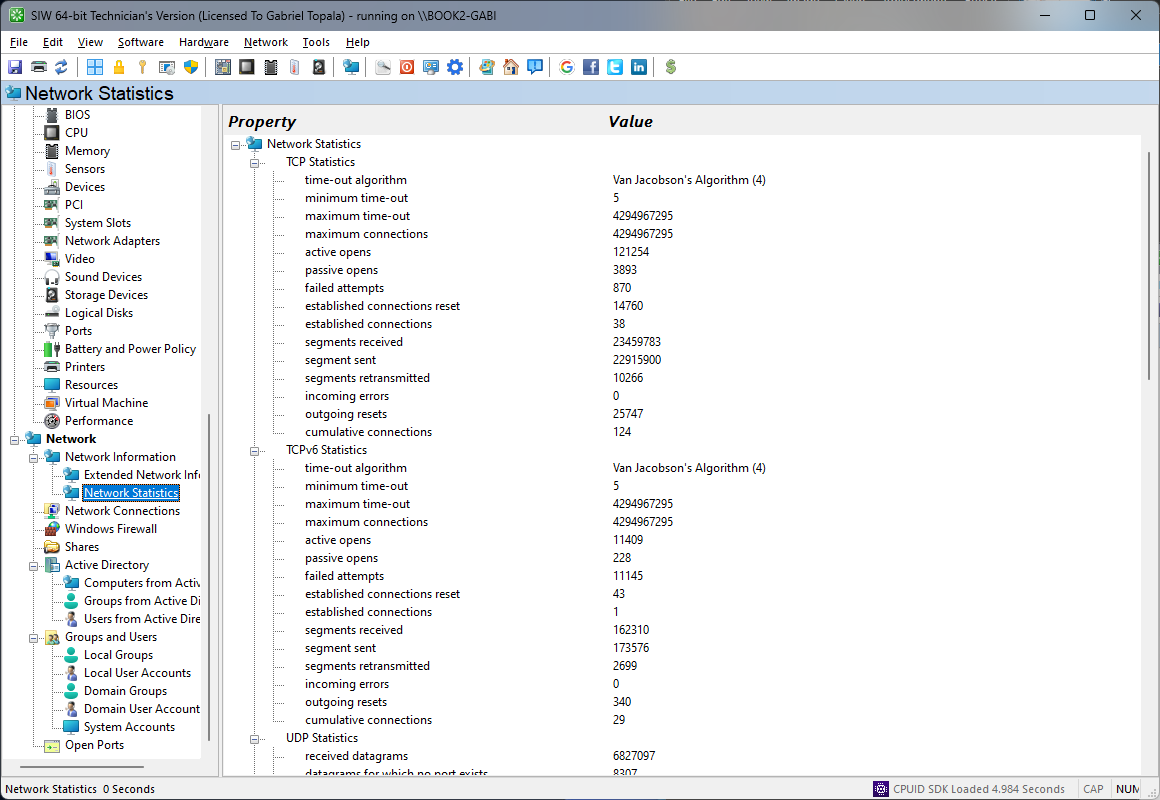
Network StatisticsTop ↑
TCP, UDP, IP, Network Parameters, Adapter Info
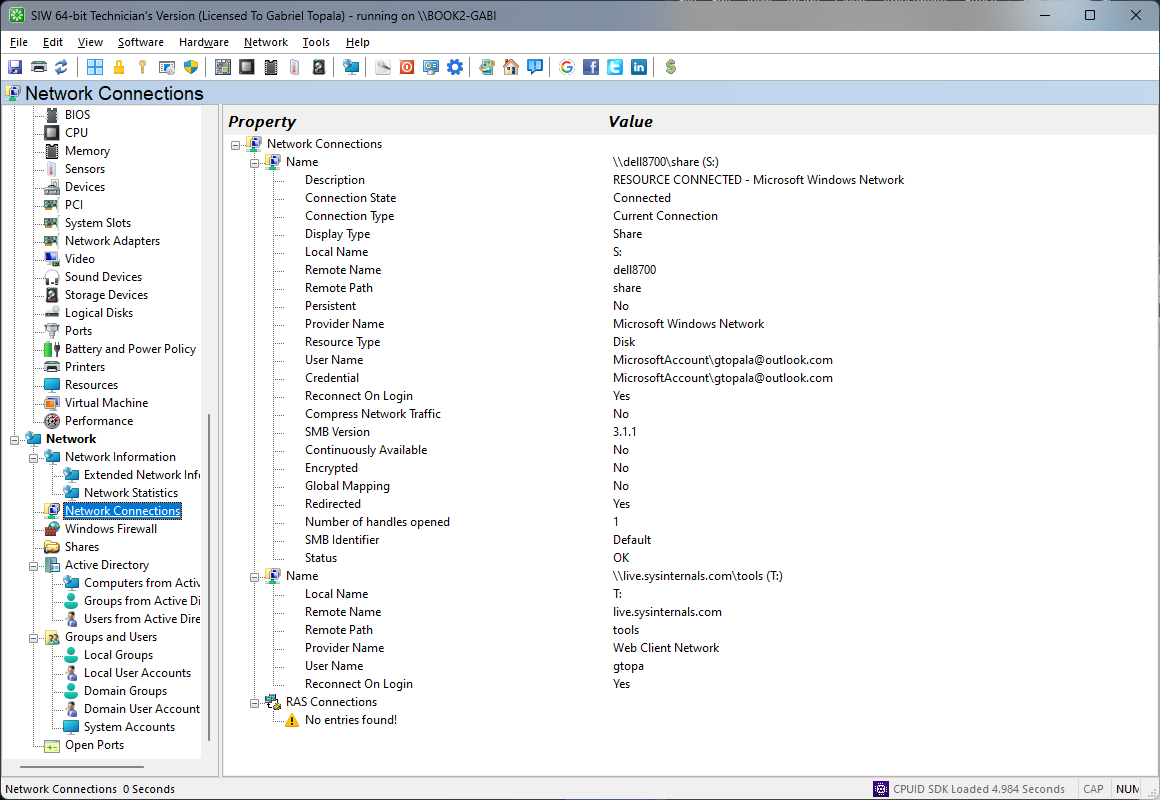
Network ConnectionsTop ↑
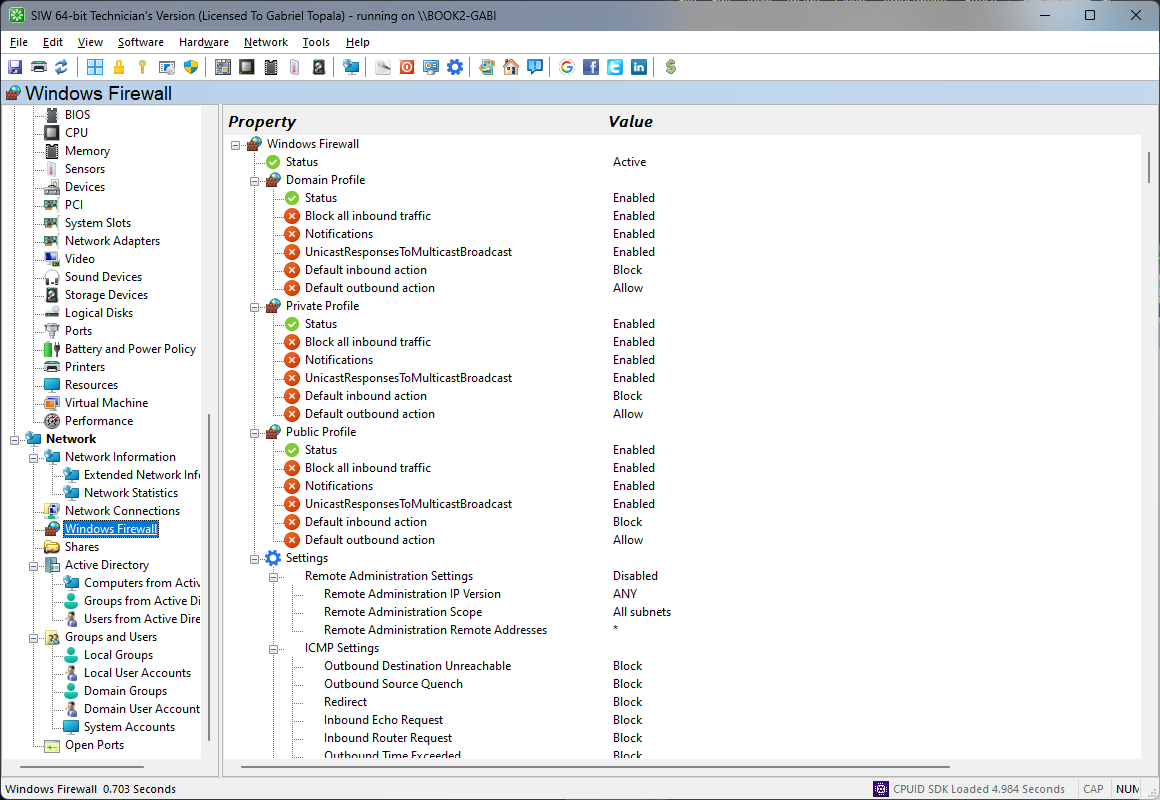
Windows FirewallTop ↑
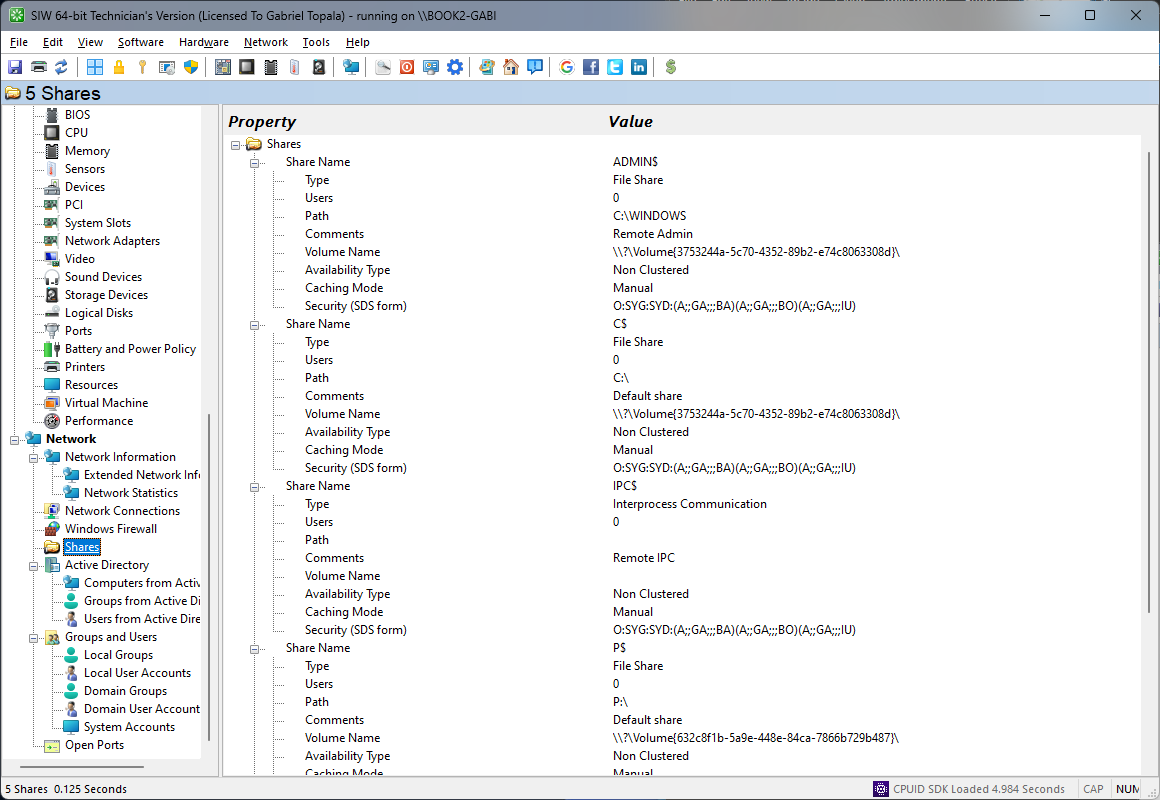
SharesTop ↑
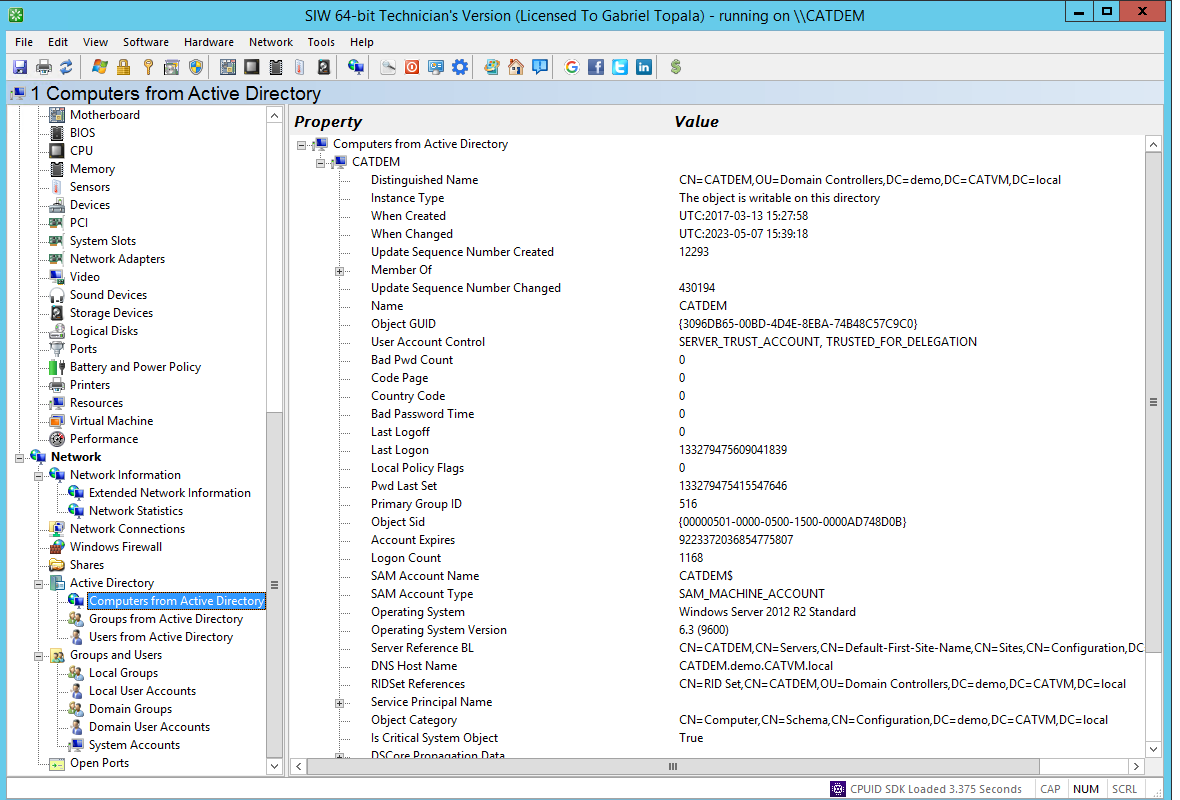
Active Directory - ComputersTop ↑
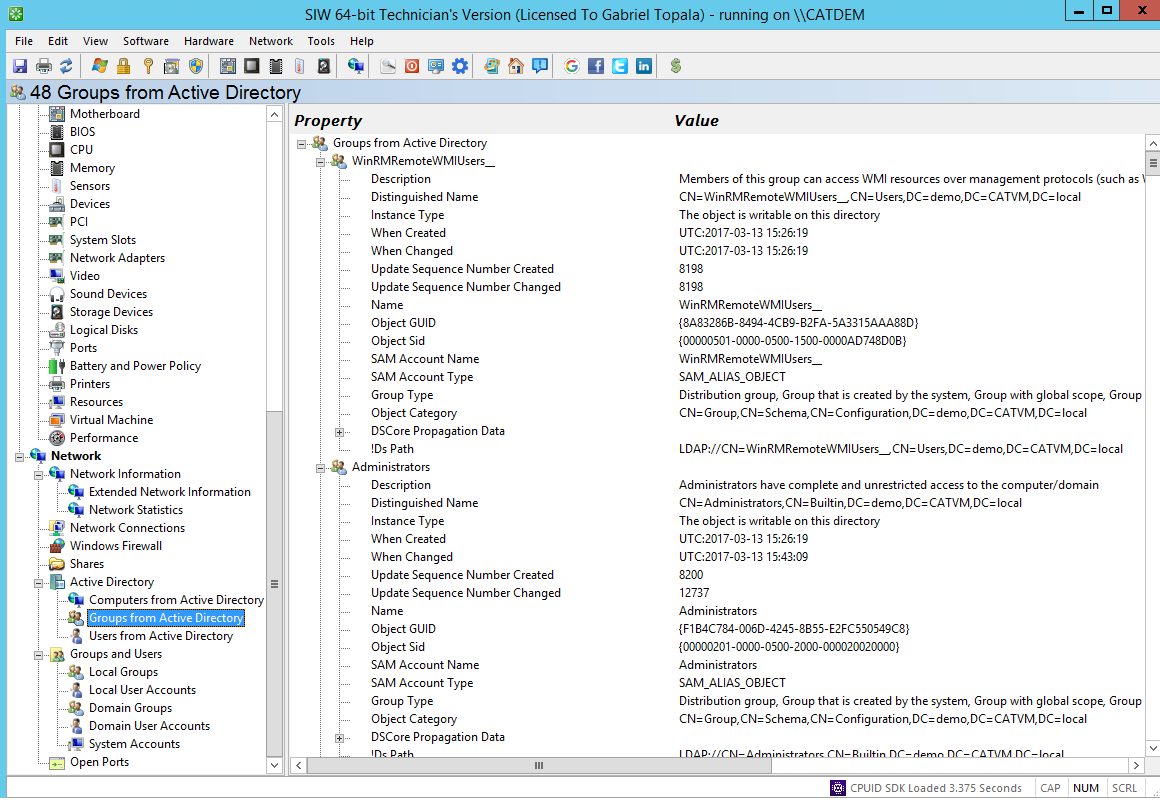
Active Directory - GroupsTop ↑
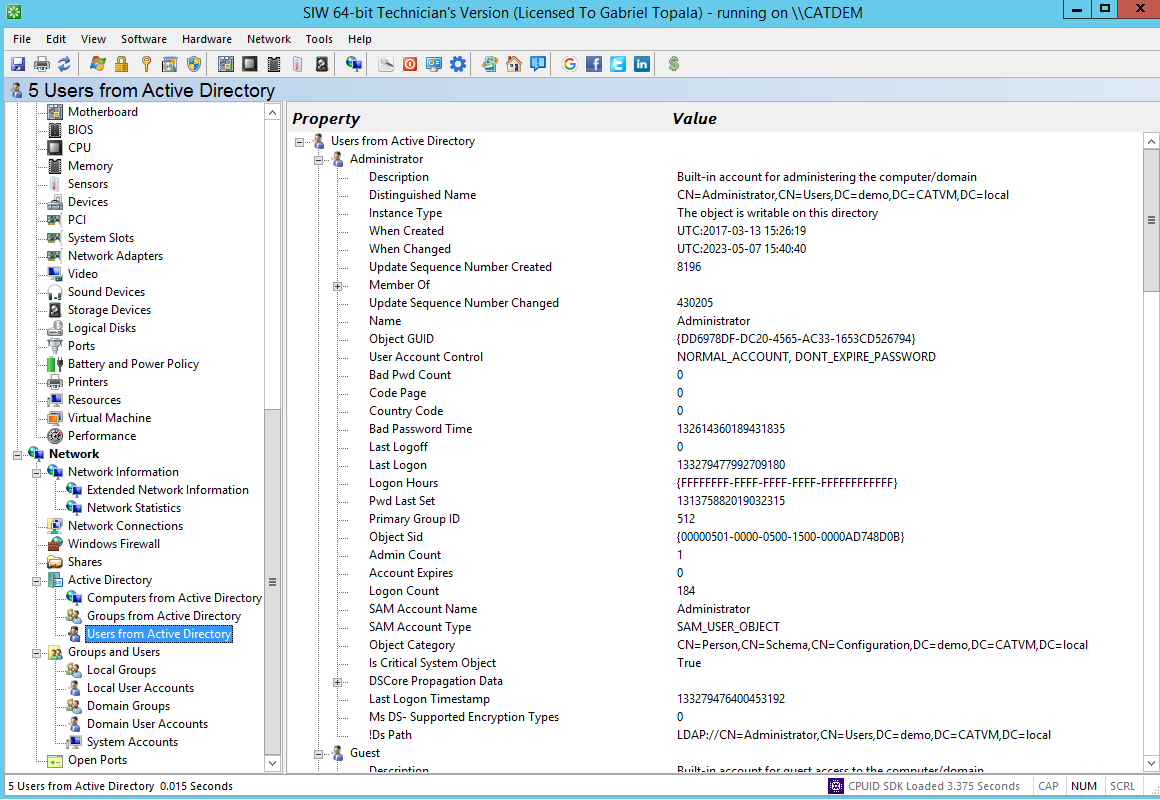
Active Directory - UsersTop ↑
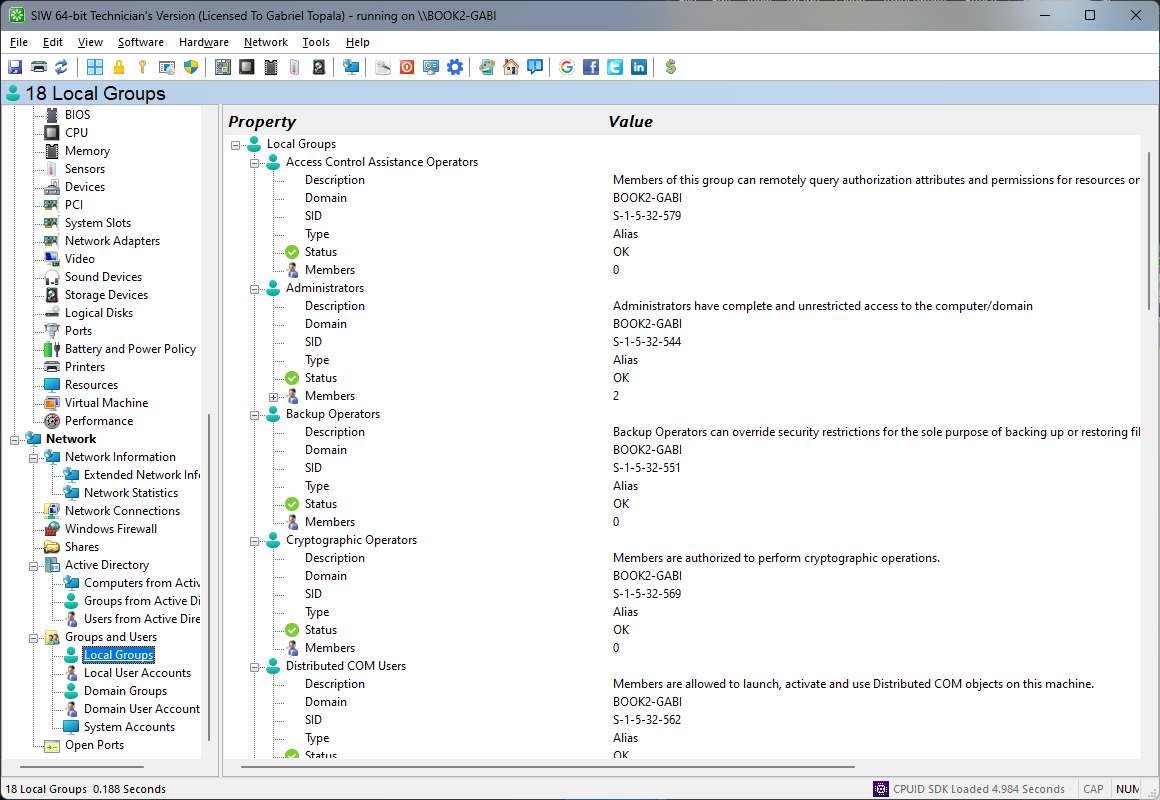
Local GroupsTop ↑
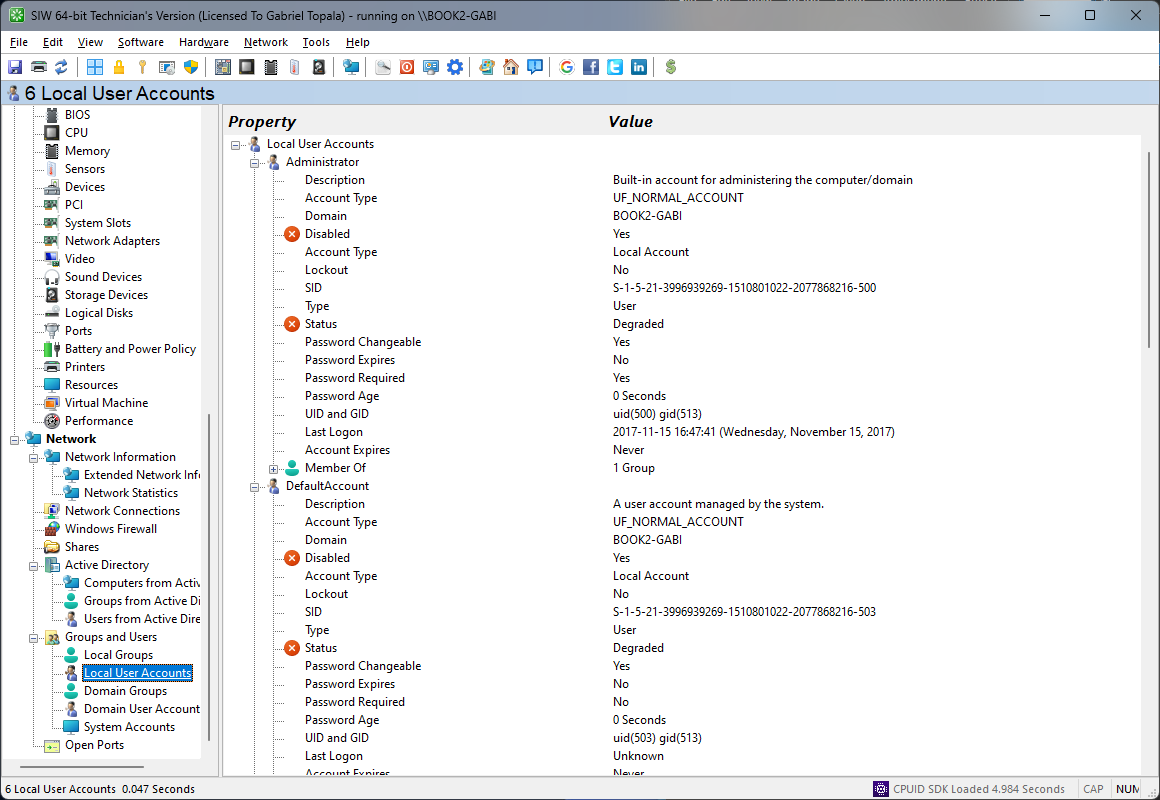
Local User AccountsTop ↑
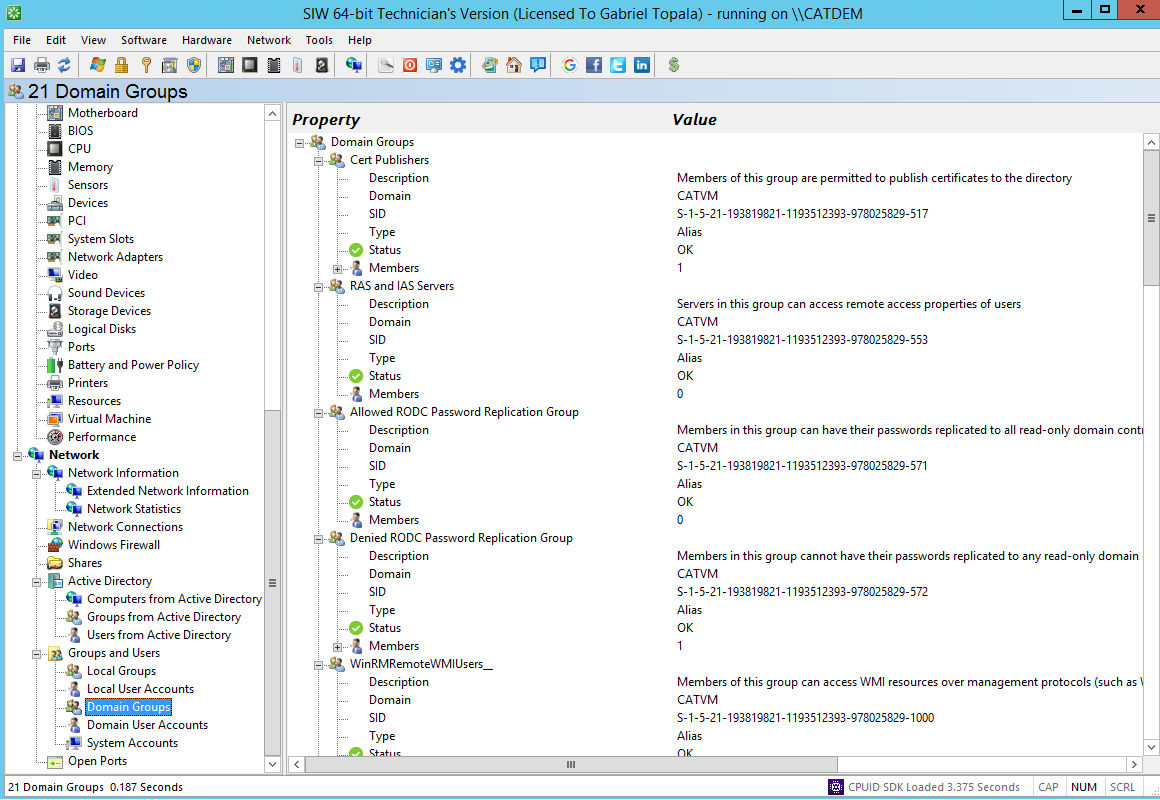
Domain GroupsTop ↑
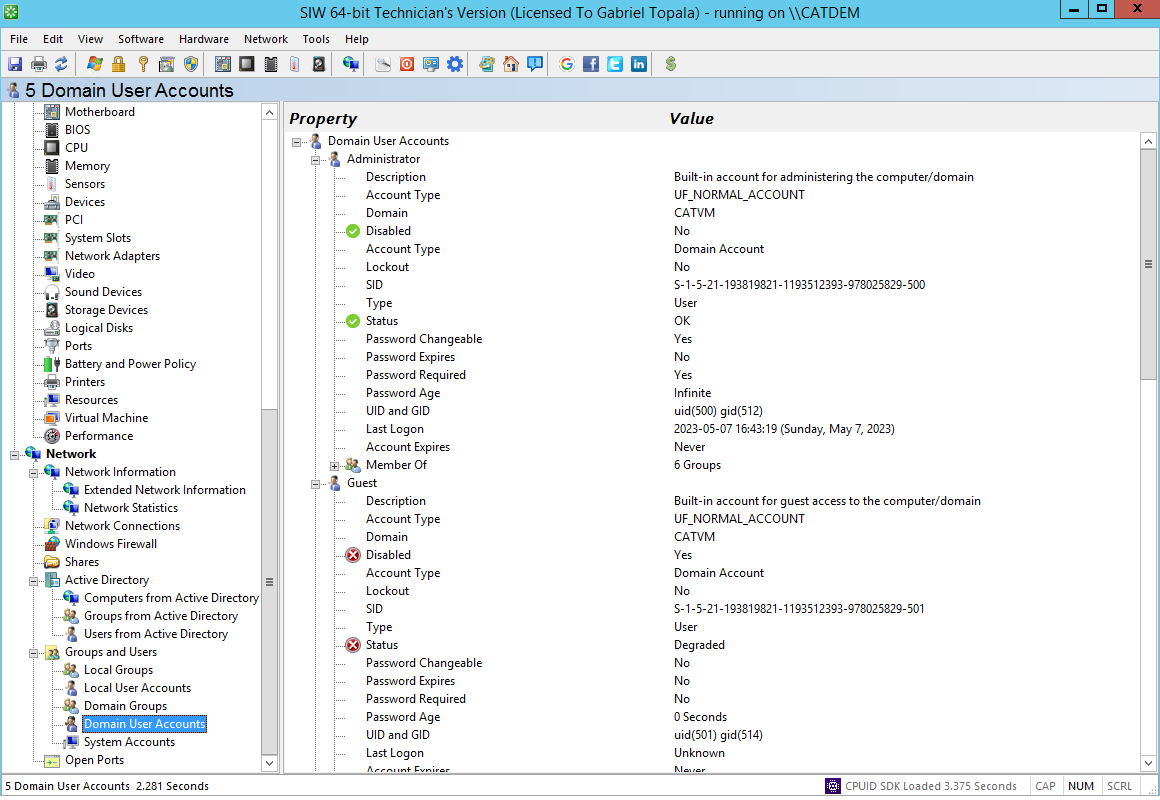
Domain User AccountsTop ↑
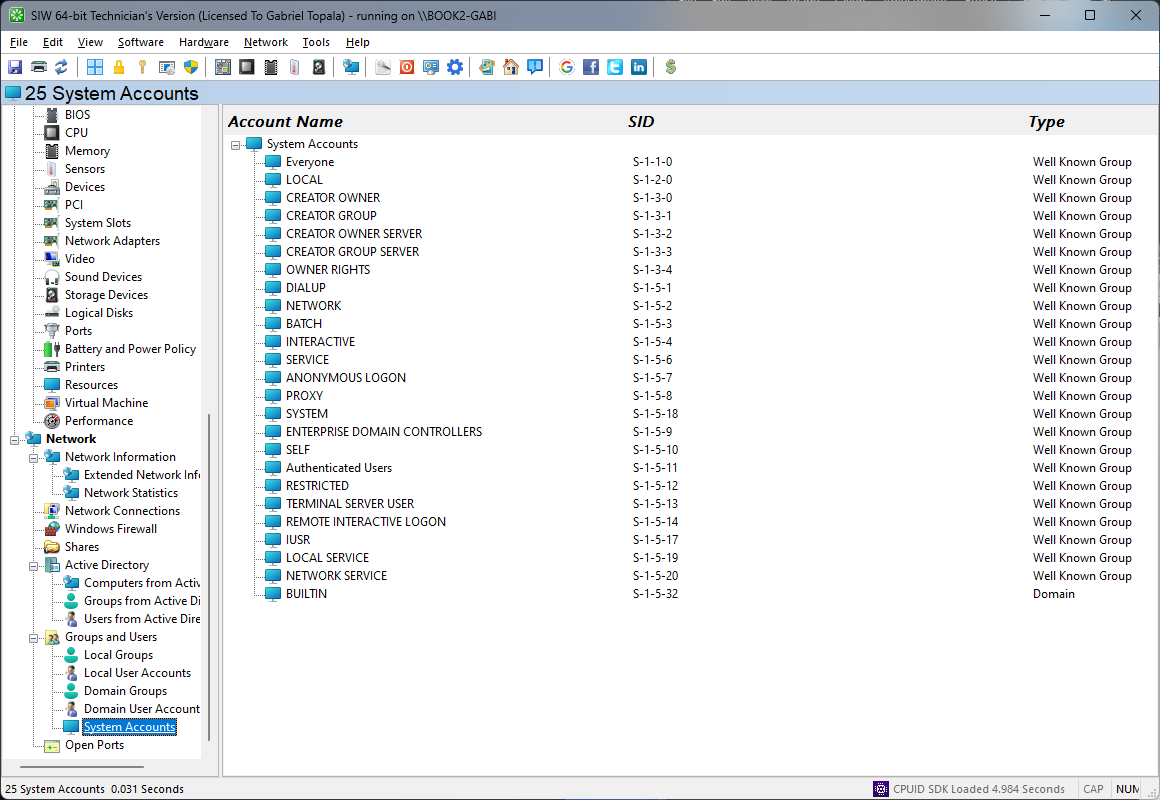
System AccountsTop ↑
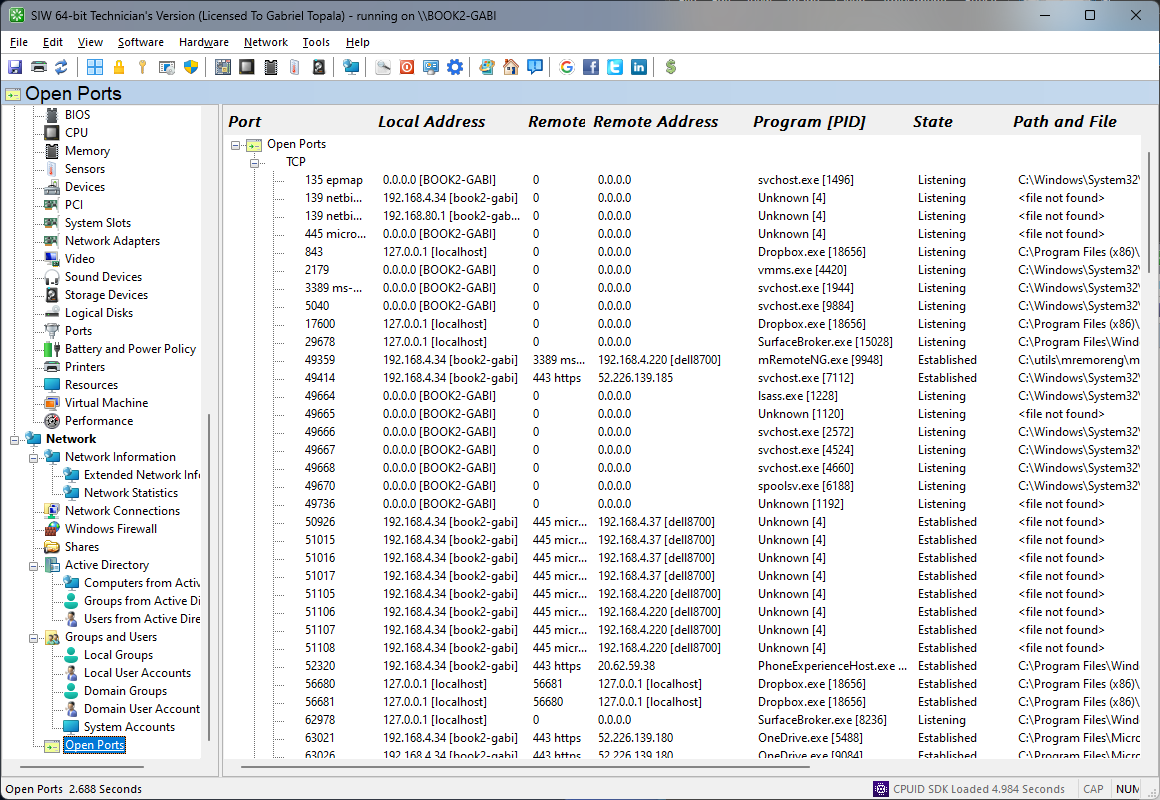
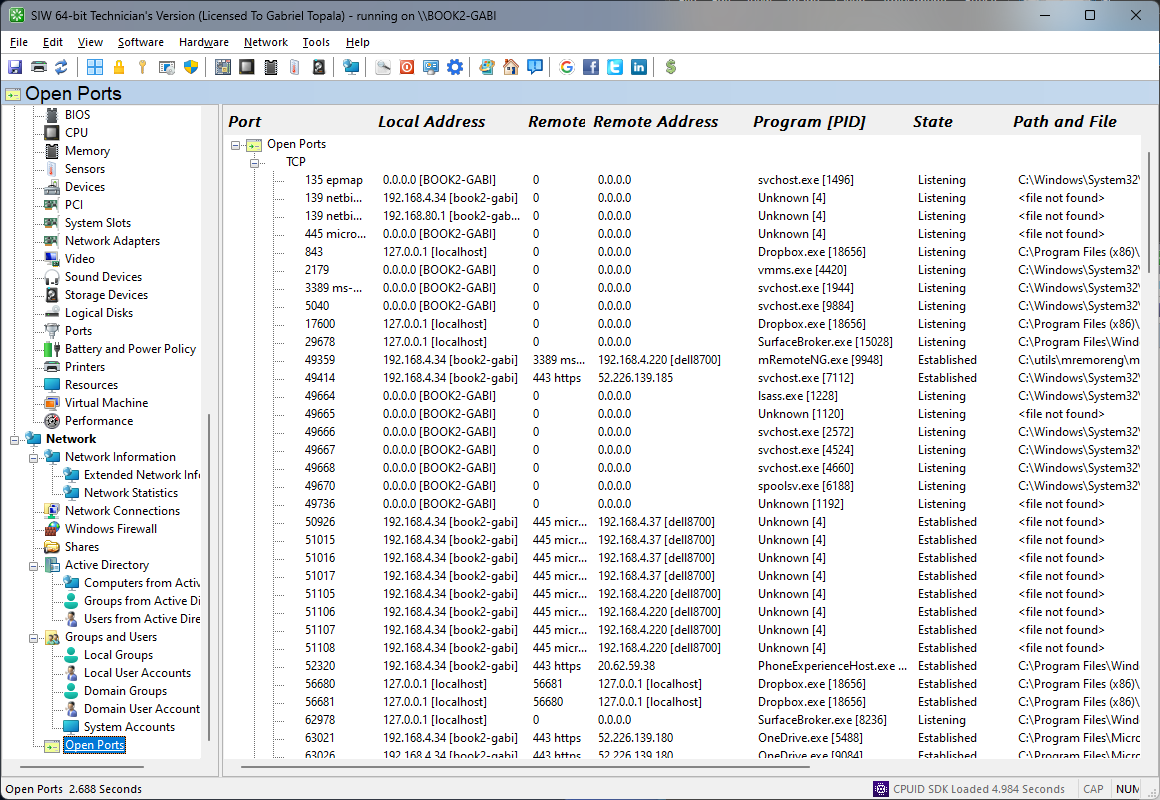
Open PortsTop ↑
SIW allows you to view a list of all TCP and UDP ports that are in use, and the application that is using it.
Additional information includes the local port name and local/remote IP address.
Using the Right-Click menu, you can close (Disconnect) a selected connection, or create a CSV, HTML, TEXT or XML report file.
Additional information includes the local port name and local/remote IP address.
Using the Right-Click menu, you can close (Disconnect) a selected connection, or create a CSV, HTML, TEXT or XML report file.